Do you know what's misconfigured in your M365 environment?
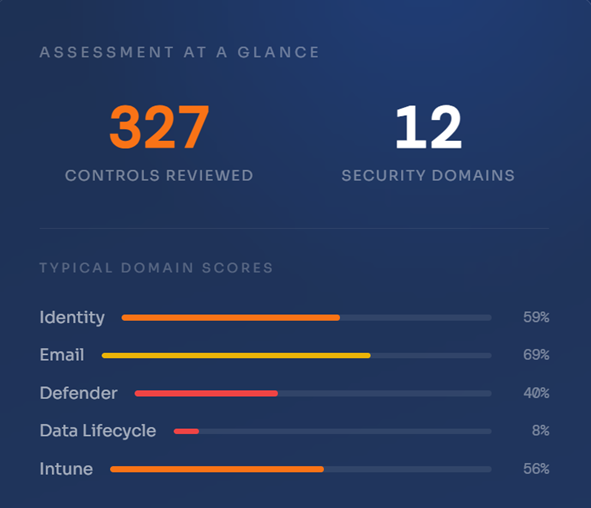
Most organisations assume their Microsoft 365 environment is secure. Our Cloud Security Assessment checks 327 controls across 12 domains. What we find is almost always surprising.
SCOPE
12 domains. Every corner of your M365 environment.
We don't spot-check. We conduct a comprehensive review across every major security domain in your Microsoft 365 tenancy.
Identity
Entra ID, MFA, Conditional Access, privileged roles & lifecycle policies
Email Security
Anti-phishing, safe links, DKIM, shared mailboxes & spam confidence
Microsoft Teams
External access, channel creation, meeting policies & cross-tenant trust
SharePoint
External sharing, idle sessions, OneDrive sync & alert policies
Microsoft Defender
138 controls inc. Defender for Endpoint, Identity, Cloud Apps & more
Microsoft Intune
Device compliance, enrolment, cleanup rules & endpoint configuration
Information Protection
Sensitivity, DLP, content marking & encryption
Data Lifecycle
Retention policies across Teams, SharePoint, OneDrive & Exchange
Defender for Office
Anti-spam, safe attachments, allowed senders & BCL thresholds
Applications
Enterprise apps, OAuth permissions & least-privilege access review
Endpoint Manager
Security baselines, ASR rules, LSASS protection & device restrictions
Secure Score
Benchmarking against Microsoft's recommended actions & target posture
PROCESS
What to expect
A structured, low-disruption engagement that fits around your team's schedule.
01 — Discovery
30-minute scoping call
We align on your environment, licensing, priorities and any known concerns. No homework required beforehand.
02 — Assessment
Read-only review
Using Security Reader and Global Reader roles, we assess your tenancy across all 12 domains. No changes are made to your environment.
03 — Report & Remediation
Scored report & clear next steps
You receive a fully scored findings report and a prioritised remediation plan your team can act on straight away.
COMMON FINDINGS
What we typically find
These aren't edge cases. We see these patterns in the majority of M365 environments we assess - regardless of team size or maturity.
⚠ High Priority
Conditional Access in pilot mode
Policies created but scoped to test groups - leaving the broader organisation unprotected.
⚠ High Priority
Defender gaps across 60+ controls
Of 138 Defender controls, the average environment has fewer than a third fully completed.
⚠ High Priority
LSASS protection not enforced
Leaves devices vulnerable to credential harvesting tools like Mimikatz.
● Medium Priority
DLP policies stuck in test phase
Sensitivity and data loss prevention policies created but never promoted to production.
● Medium Priority
No data retention policies
Teams, SharePoint and OneDrive left without retention rules — creating regulatory exposure.
● Medium Priority
Stale accounts in Entra ID
Disabled accounts never removed, no lifecycle policy configured for regular review.
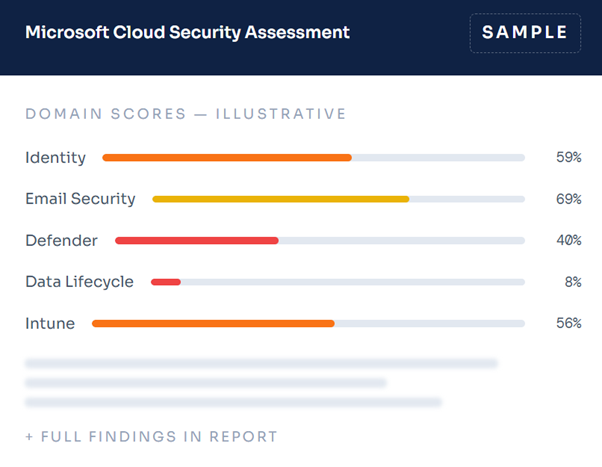
SAMPLE REPORT
See exactly what a real assessment looks like
We've made a real assessment report available to download. It covers findings, scores and prioritised recommendations across all 12 domains - so you can judge for yourself whether it's the right fit for your environment.
BOOK A CALL
Let's talk about your environment
A 30-minute discovery call is all it takes to understand what an assessment would cover for your specific environment - the scope, the process, and what you'd walk away with.
-
No preparation needed on your end
-
Read-only access - nothing in your environment will be changed
-
You'll receive a fully scored report and prioritised remediation plan
-
No lengthy statements of work or drawn-out engagements
FURTHER READING
While you're here...
BLOG POST
Zero cost, minimum effort - top ways to secure your M365 environment
Ten practical steps your team can take today, at no cost and without raising a change request.
SERVICES
Explore our full range of cybersecurity services
From Cloud Security Assessments to Dark and Deep Web Intelligence and ongoing managed security, see how Talanos can support your team.
View services